In the third of a four-part series of articles examining how data is a valuable asset as well as a business risk for organisations, Laurence Pitt, the director of security strategy for EMEA at Juniper Networks, explores the new security threats to data – and the new rules for organisations to follow.
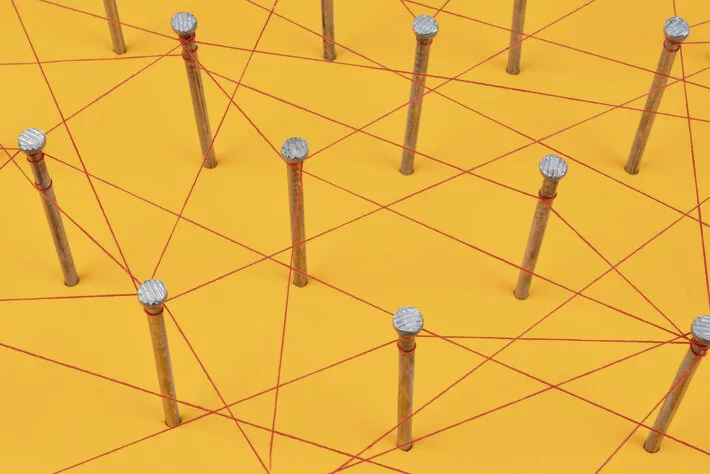
Securing data inside a perimeter is a relatively easy task. But who operates within a perimeter these days? Datacentres, public cloud, private cloud, business application hosts – your data resides in them all and in today’s world, there is no perimeter. So as a CISO, ask yourself this: why is your organisation still playing by the old rules of perimeter security when the perimeter no longer exists? The network is the common factor that connects everything, so why not consider the network as a key component of your security?
You own your data and, under GDPR, you need to know where that data is and what applications are using it at any given point in time (in a recent poll Juniper conducted, 43% of respondents admitted they did not know where their data is stored). But you use many third parties to store, transport and retrieve your data so how do you define the boundary of your network? And your organisation needs access to this information in real-time to enable business agility and faster decision making. As much as we may instinctively want to lock the systems down Fort Knox-style, this defeats the object of collecting the data in the first place.
But as we’ve mentioned, not all data is created equal, so investing in a blanket approach to security may not be cost-effective nor operationally expedient. How would your security posture change if you knew where your most valuable data was stored? By having intelligence in the network and investing in real-time security, you can have a better overview of what’s going on and can respond accordingly. You can balance the level of investment against the relative value of specific data.
Key takeaways
- Perimeter security is no longer a viable option, instead focus on securing the network.
- Avoid locking systems down, this defeats the object of collecting data for an agile business.
- Balance investing in security with the value of sub-sets of data that is to be secured.